An abortion rights hacktivist group says it launched cyberattacks against Arkansas and Kentucky state governments and leaked files from their servers to protest their bans on abortion after the U.S. Supreme Court’s recent decision to overturn Roe v. Wade.
The group, which calls itself SiegedSec, said it hacked the two states because it was angry about their bans.
“THE ATTACKS WILL CONTINUE!” the group posted on a Telegram channel. “Our main targets are any pro-life entities, including government servers of the states with anti-abortion laws.”
While the group claims it leaked internal documents and files with employee personal information, Arkansas and Kentucky state officials say initial reviews found that none of the documents were thought to be sensitive or non-publicly available.
Cybersecurity experts say they expect to see additional attacks against states by hacktivists angered by abortion bans.
“This is a legitimate threat that states need to take seriously,” said Dan Lohrmann, a chief information security officer at Presidio, a global digital services and cybersecurity company. “It’s an important issue. It’s likely there’s going to be more of these hacktivist attacks to come.”
In recent years, state and local governments have been targets of hacktivism, a blend of hacking and activism for a political or social cause. Unlike cybercriminals, who hack into computer networks to steal data for money, most hacktivists are individuals or groups of hackers who band together and see themselves as fighting injustice.
Hacktivists have launched attacks on everyone from foreign governments and corporations to suspected drug dealers and pedophiles. Police departments and hospitals also have come under attack. Hacktivists have frozen government servers, defaced websites and hacked into data or email and released it online.
Since Russia’s attack on Ukraine in February, hacktivist groups on both sides have stepped up attacks. A Twitter post from an account named “Anonymous,” a loosely associated network responsible for attacking government, corporate and religious websites, for example, urged hackers around the world to target Russia.
Hacktivists often launch cyberattacks against state or local governments after a major, controversial event or decision, such as the fatal police shooting of a Black man or the water crisis in Flint, Michigan.
In the case of Arkansas and Kentucky, both have abortion ban laws that immediately went into effect after the Supreme Court’s June 24 ruling.
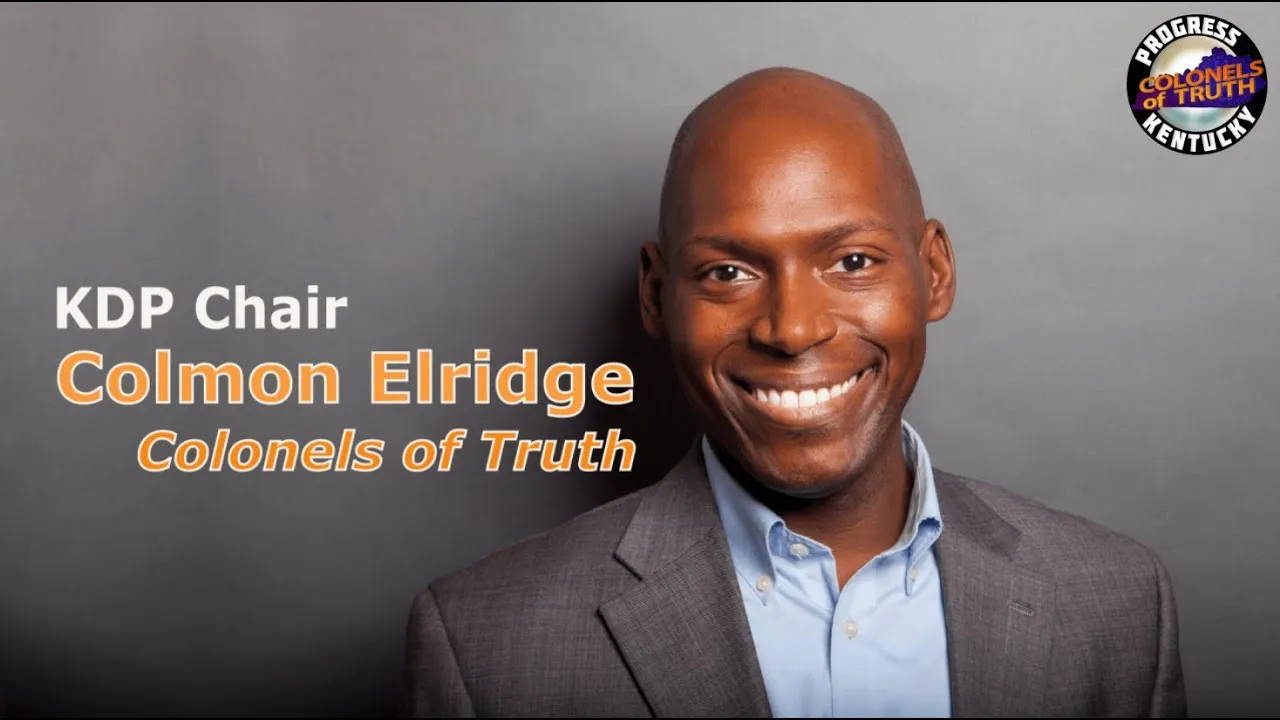
Jill Midkiff, spokesperson for the Kentucky Finance and Administration Cabinet, said the Commonwealth Office of Technology is investigating the hacktivist group’s claims about its impact.
“Information pertaining to Kentucky has been identified and while initial indications are that this is publicly available data that does not include personally identifying information, the state will continue its investigation,” she said in an email.
The information that was accessed, she added, was on a single folder on a state server that was used to house “publicly accessible documents linked directly from a publicly accessible state website.”
Federal law enforcement agencies have been notified, Midkiff said, and the technology office’s information security officers “remain on high alert.”
In Arkansas, Shealyn Sowers, spokesperson for Republican Gov. Asa Hutchinson, sent Stateline a statement that said the state Division of Information Services became aware last week of the hacktivist group’s claim to have accessed and downloaded internal documents from state systems.
“After initial analysis, our security teams have determined that there was no access beyond what is publicly available and only public record data was seen or downloaded,” Sowers said. “The systems that were involved did not sit on the State of Arkansas network but rather in a public cloud provider.
“We continue to remain vigilant as we go about the process of keeping our systems secure,” she added.
Brett Callow, a threat analyst for cybersecurity company Emsisoft, said he’s not surprised states with abortion bans were targeted.
“States that are legislating against abortion rights are potentially going to be in the crosshairs of hacktivists,” he said. “I would be very surprised if this were to be an isolated incident. This is pretty much as contentious as it gets.”
Abortion is expected to become illegal in more than two dozen states as a result of the Supreme Court’s ruling, according to the Guttmacher Institute, which advocates for abortion rights.
And while many states have banned abortion, others have shored up abortion rights and protections. That could make them vulnerable to anti-abortion hacktivists as well, Lohrmann said.
“I think you’re going to have both sides potentially launching hacktivist attacks,” said Lohrmann, a former chief information security officer for the state of Michigan. “States need to be on the alert, doing due diligence and looking for any unusual activities.”
--30--
Written by Jenni Bergal. Cross-posted from Stateline, an initiative of The Pew Charitable Trusts.